How to Block External Access to the XenMobile Self Help Portal & NetScaler Gateway Page
 by Daniel Ruiz, Senior Solutions Architect
by Daniel Ruiz, Senior Solutions Architect
XenMobile 10 is mostly configured with the Citrix NetScaler to load balance Mobile Device Management (MDM) traffic to the XenMobile Servers (XMS), as well as to host the micro VPN connectivity utilizing the NetScaler Gateway. One of the features that is enabled by default is the Self-Help Portal which is typically utilized to allow users to manage their own devices.
While this is helpful and usually cuts down on the administrative overhead, it does not however allow for second factor authentication and also exposes single factor LDAP logins externally though the MDM LoadBalancer VIP on 443. From a security perspective this raises a red flag and can be a challenge to fix.
The first part to remedy this is to leverage NetScaler responder policies to block specific portions of the MDM sites when traffic is coming from the outside and still allow internal access to the sites based on specific LAN defined subnets.
The second part is to hide the NetScaler Gateway Page, which by default will simply display your traditional NetScaler Gateway authentication with user name and LDAP password. You can use another responder policy that will respond with a blank HTML page, yet still allow the devices to VPN and enroll.
Blocking External Sites:
Create a new SSL offloadMDM VIP. By default, the NetScaler Wizard creates an SSL Bridge where responder policies cannot be applied.
Follow this article from Citrix (CTX218327) on how to apply the XenMobile MDM SSL Offload Configuration.
Once your configuration on the XMS and NetScaler MDM VIP is set to SSL Offload, we need to create a responder policy and apply it to the new MDM SSL 443 offload VIP just created.
Syntax:
add policy patset XMS_UrlSet
bind policy patset XMS_UrlSet “/zdm/shp/console” -index 6
bind policy patset XMS_UrlSet “/zdm/login_xdm_uc.jsp” -index 5
bind policy patset XMS_UrlSet “/zdm/helper.jsp” -index 4
bind policy patset XMS_UrlSet “/zdm/log.jsp” -index 3
bind policy patset XMS_UrlSet “/zdm/login.jsp” -index 2
bind policy patset XMS_UrlSet “/zdm/console” -index 1
add responder policy resp_xms_admin_shp_drop_pol “CLIENT.IP.SRC.IN_SUBNET(10.10.1.0/24).NOT && CLIENT.IP.SRC.IN_SUBNET(172.10.1.0/24).NOT && HTTP.REQ.URL.STARTSWITH_ANY(\”XMS_UrlSet\”)” DROP -comment “Created by Daniel Ruiz”
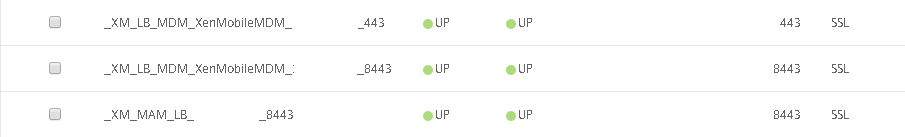
bind lb vserver _XM_LB_MDM_XenMobileMDM_443 -policyName resp_xms_admin_shp_drop_pol -priority 100 -gotoPriorityExpression END -type REQUEST
bind lb vserver _XM_LB_MDM_XenMobileMDM_8443 -policyName resp_xms_admin_shp_drop_pol -priority 100 -gotoPriorityExpression END -type REQUEST
In the syntax above, I am specifying 2 subnets (10.10.1.0/24 and 172.10.1.0/24), if the traffic does not originate from both subnets, the traffic will be dropped.
Once the responder is set, bind it to the 2 new MDM SSL Offload VIPs for 443and 8443.
Hiding the XenMobile NetScaler Gateway Site:
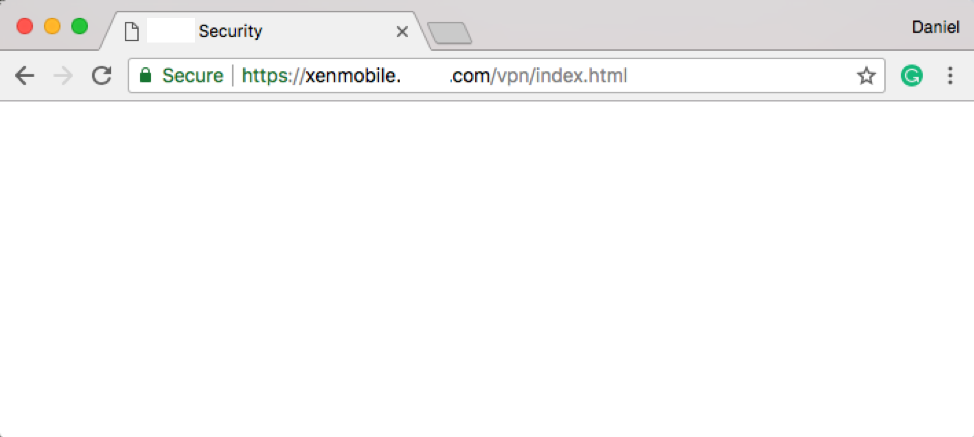
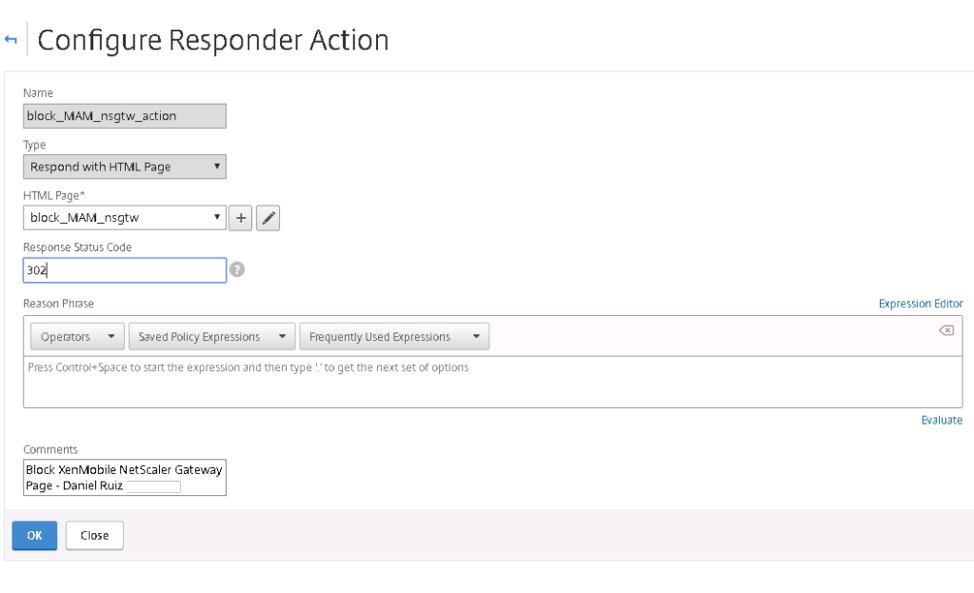
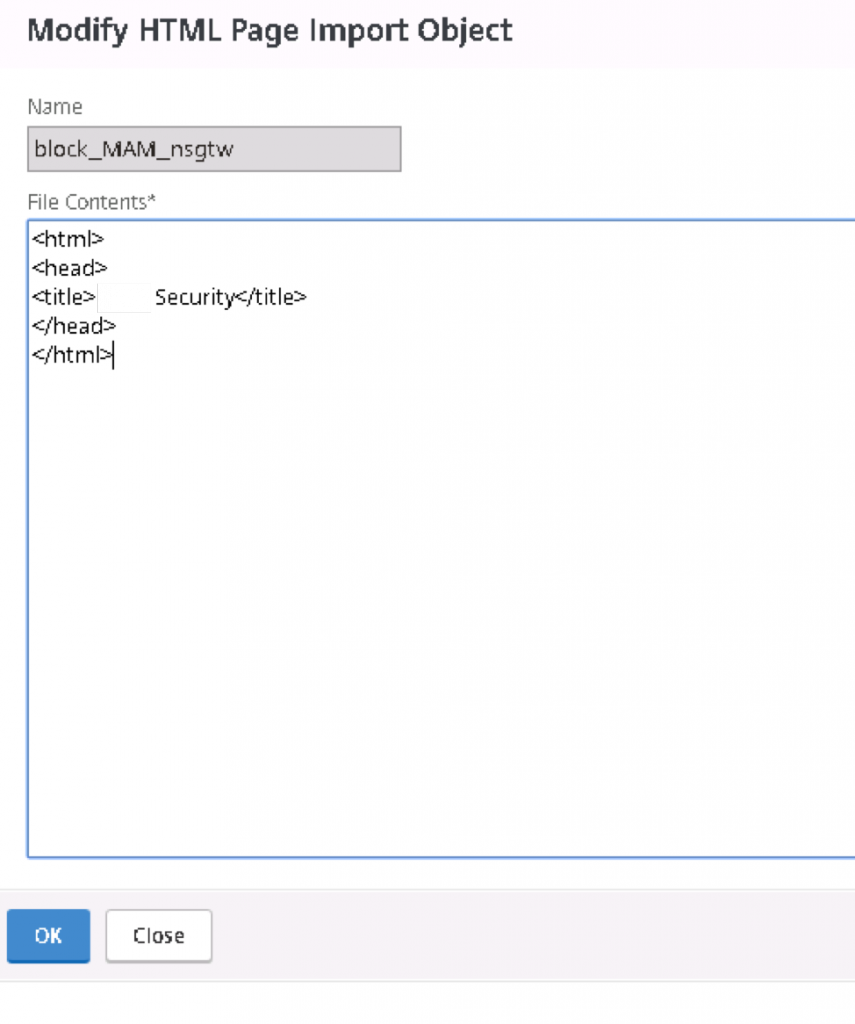
A responder action needs to be set in order to respond with an HTML page, which in this case presents a blank page when connecting to the NetScaler Gateway.
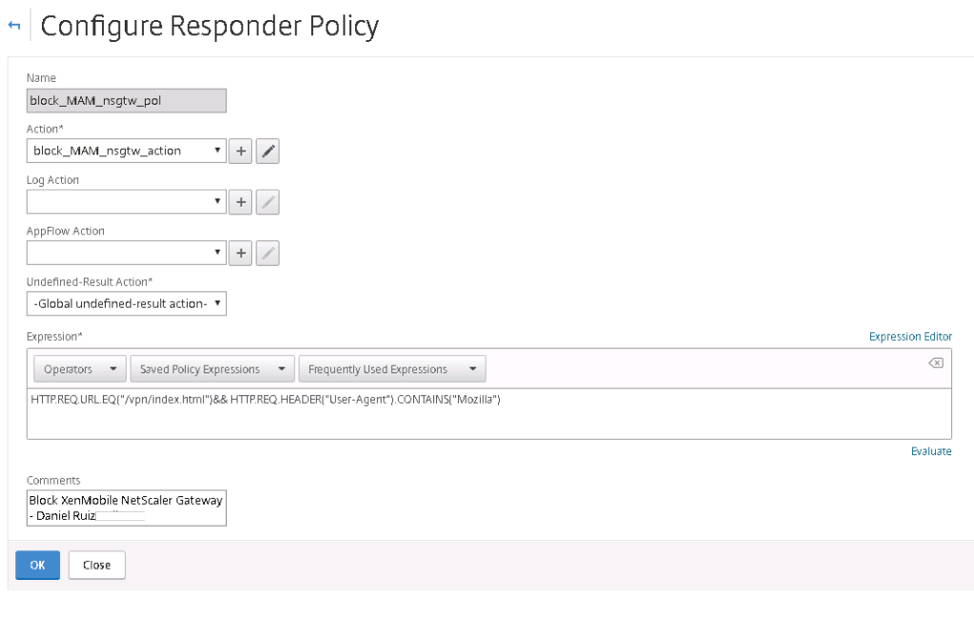
The responder policy below will be binded to the action and will look for the /vpn/index.html page of the XenMobile NetScaler Gateway.
Syntax:
add responder action block_MAM_nsgtw_action respondwithhtmlpage block_mam_nsgtw -comment “Block XenMobile NetScaler Gateway Page – Daniel Ruiz”
add responder policy block_MAM_nsgtw_pol “HTTP.REQ.URL.EQ(\”/vpn/index.html\”)&& HTTP.REQ.HEADER(\”User-Agent\”).CONTAINS(\”Mozilla\”)” block_MAM_nsgtw_action -comment “Block XenMobile NetScaler Gateway – Daniel Ruiz”
bind vpn vserver _XM_XenMobileGateway -policy block_MAM_nsgtw_pol -priority 100 -gotoPriorityExpression END -type REQUEST
Below is a screenshot of the end result. When accessing the XenMobile Page, the HTML content of the responder action will be displayed.
 If you have any questions or need additional information, please contact service@helient.com.
If you have any questions or need additional information, please contact service@helient.com.